Data breach! How many times have you become a victim? How many of you have become a victim? It can happen to anyone, anytime!
The reason why I am writing this article today is that between 5 PM and 6 PM today, I received a series of emails from Amazon (yes, that online shopping site).
The emails contained horrible sights.
Someone tried to buy Gift Cards worth around $300 (about 22,000 in Indian currency) from the account.
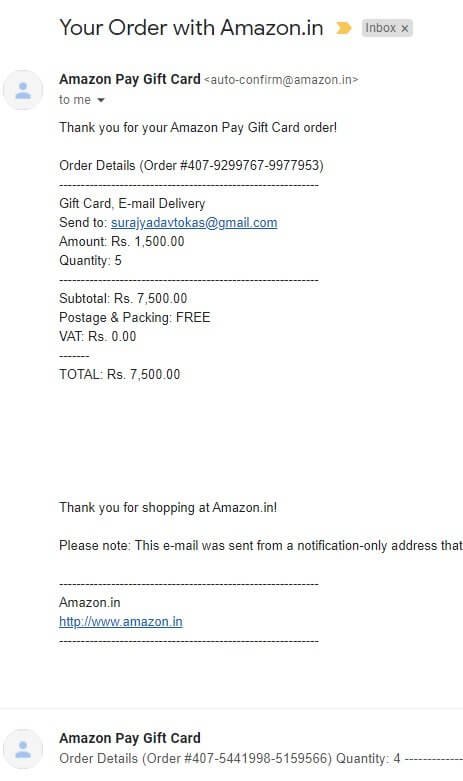
The person who did this archived every order he placed. You can see the email ID of that person. It is surajyadavtokas@gmail.com.
Fortunately, all the cards they tried were either expired or replaced with newer upgraded cards, or had online transactions turned off.
What’s interesting is that I am extremely meticulous about keeping my passwords safe. I also ensure that I use very strong passwords that contain letters, numbers, special characters, etc.
Still, someone managed to get into my Amazon account and attempted that horrible thing!
How did someone get access to my Amazon account?
I don’t know!
Maybe someone used a keylogger to log my keystrokes to get the password.
That’s highly unlikely because that would make all my passwords vulnerable. On top of that I use a powerful antivirus program (Kaspersky) that can detect such activities.
Possibly someone hacked into my system.
That’s unlikely, but not impossible. If someone hacked into my computer, that person has to go through a secure vault that locks all my passwords.
I later discovered that the password for Amazon and a few other sites (that I no longer use) were saved in LastPass – a password managed that was breached. I never bothered to change the password for Amazon.
That gave access to my Amazon account to the perpetrator (possibly).
On top of that, I never cared to enable Two-Factor Authentication on Amazon.
This event alone was enough for me to take corrective steps.
I went through every freaking account for every service I use, and changed the passwords. I also enabled Two-Factor Authentication for every service that allowed me to do so.
Now, I have kept all the passwords in a separate device that is not connected to the Internet.
I was lucky to get away with this.
Will you be lucky enough?
That’s the reason why I am writing this article even after these things happened to me today:
- I went for my scheduled doctor visit.
- Had two of my cats neutered.
- Shocked to the core by looking at those emails.
- Changed all the passwords.
Though I am totally exhausted, I still want to write this. I don’t want any of you to go through this ordeal.
It is better to be safe than sorry!
Let’s start by answering a few questions before I tell you how to create secure passwords.
How does someone get access to your password?
One of the core reasons why cyber criminals manage to get access to our passwords is that you and I are fools.
We are fools because:
- We often set easy passwords.
- We don’t change our passwords quite often.
- We often store our passwords in browsers (yes, all modern browsers can do that).
- We often resort to password managers like LastPass that are themselves not very secure.
If you have ever used a password manager, you will know that those programs will allow you to store passwords for different websites; store your banking details like credit/debit card details, banking account ID and password; etc.
Have you ever wondered, what happens if they get hacked? Who guarantees their security?
That’s one of the main reasons why I don’t recommend using password managers in the first place. If you absolutely want to use password managers, use the ones that are extremely secure. I recommend using Dashlane.
But I will still repeat – try and avoid using password managers.
They may make your life easy, but you are never truly safe!
Now, coming to the point:
How does someone get access to your password?
Unless you yourself hand over your user ID and password to someone, it shouldn’t be accessible to others.
But cyber criminals have a few tricks up their sleeves that they use for hacking passwords.
Let’s check the methods!
Method 1: Buy passwords
One of the easiest tricks is to buy passwords off the dark web. That’s a very dark place. There is big money involved in buying and selling login credentials.
Security breaches keep happening. Someone may successfully breach some online service and sell the stolen info on the dark web for a high price.
If you haven’t changed your passwords for a very long time (years), the chances are that your passwords have been compromised.
That’s the reason why it is strongly suggested that you keep changing your passwords at regular intervals. This will ensure that hackers have to crack your passwords, instead of simply using the credentials they purchased online. In that case, they will try one of the methods mentioned below.
Whatever happened to me today was possibly this scenario. I never bothered to change the password for my Amazon account since 2014. LastPass had a security breach in 2015 that exposed the credentials of thousands of users.
I still did not care to do anything!
This possibly came back to haunt me!
Don’t be like me. Only if I had taken some time to change my Amazon account credentials, the incident that happened today would have never happened.
Method 2: Brute Force Attack
This is the commonest form of attack that a cyber criminal will deploy first. Brute Force uses every combination in the book until the hacker gets to your password.
The whole thing is automated, and the software tries out as many combinations as possible in as little time as possible.
Sounds laborious?
Think again! There has been significant development in this technology, and in 2012, a hacker showed a 25-GPU cluster capable of hacking any 8-character password for Windows in less than six hours. It didn’t matter whether the password uses upper or lowercase letters, symbols, and numbers.
What he showcased could try a whopping 350 billion combinations every second!
You know what? As long as your password is up to 12 characters, you are at risk.
If there is something that brute force attacks teaches everyone then it is this – ‘Ensure that your passwords are at least 13 characters long! The longer the better.’
All passwords that I have set today have 45 characters each with lowercase and uppercase letters, symbols, and numbers.
With such long passwords (if not totally impossible to crack), brute force attacks will take a very long time to get the right combinations!
Method 3: Dictionary Attack
This isn’t really a smart route for hackers, because there is a way to beat this format of attack. A dictionary attack is exactly what it sounds. In a dictionary attack, a prearranged list of words are used for finding passwords. These words are found in a dictionary.
In case you use a regular word such as ‘something,’ you are so very screwed! The attacker will find your password.
You need to use a word that is so uncommon that dictionaries might not include them at all, or even if they do, the software used for this attack doesn’t include the word in the list.
The best way to beat a dictionary attack is to use multiple words as a single phrase. For instance, you can use LanguishTerribleMortalityDumb.
Here is how it works:
- Use four very uncommon words that are not in the top 10,000 or top 20,000 English words.
- If necessary, create a word.
Now, when you are using four words, make sure that the total length of the password is more than 12 characters. This will prevent a brute force attack from cracking your password.
The dictionary attack on the other hand will usually limit itself to the top 10,000 or 20,000 words in English.
When you use four words, it means that the number of possible combinations will be:
10,0004 or 20,0004.
Put in simple words, the number of possible variations that the hacker has to use is the total number of words you can possibly use to the power of the number of words you are actually using.
Imagine what happens when you have one word that you made up! That word will not be in the dictionary. So, cracking your password will be impossible using dictionary attack, because of that one made-up word.
Things will become even harder when you throw in a special character somewhere in there along with one or two capitalized letters.
Now, the hacker needs to find out the exact position of that special character along with the capitalized letter (or two) and the position of the capitalized letter. That becomes infinitely more difficult for the hacker.
The tactic you use for beating the dictionary attack can be extended to beat the brute force attack as well.
Method 4: Phishing
This is one very super-nasty method! A hacker will try to intimidate you, or pressurize you, or trick you into giving up your password by taking actions that they want you to take.
You may see emails or text messages impersonating a service (such as your bank) stating that there is something wrong with your account or your plastic money (cards).
The mail will contain a link. Clicking on the link will take you to a web address where you will see a website that will, at the first glimpse, look like the actual website of the true service provider.
The moment you enter your login credentials, you are screwed! The hacker will have what he or she wants from you.
Phishing attacks are not just email or text message based. You can get calls as well. Be careful about that. I receive such calls at least two to three times a week. I play along until they ask for some sensitive data like my card’s CVV number.
Trust me, no bank ever asks for such details! If you are receiving a genuine call from a bank, they will most likely have your registered number, and that will give them all the information they need for your account. They will not ask for any such information.
Okay, now that you know how passwords are hacked, it is time to learn how to create secure passwords.
Ready?
Learn Your Password’s Anatomy
You can outsmart hackers easily. They are people like you and me. Only difference is that they use a set of rules for cracking passwords. Your job will be to set passwords that don’t follow the rules.
Step 1: Stop being silly
Most of the time our passwords are hacked because we are silly. If you are using passwords like…
- 1234
- 123456789
- 111111
- QWERTY (or qwerty)
- Password
- Password1234
- abc123
- You name followed by your year of birth
- Jesus
- Your birthday (in any format like dd/mm/yyyy, or mm/dd/yyyy, etc.)
…just close your account. It is shameful!
You have probably been hacked a million times by now.
Please don’t use passwords like that! With passwords like these, it is easy guess-work for hackers.
Step 2: Can your password be brute forced?
A brute force attack works great for passwords that are 8 characters long. It can work even for passwords that are 12 characters long.
The first golden rule here is to set your password length anywhere between 15 and 20 characters. It will be even better if you set it to be longer.
The second golden rule is to make it harder for hackers to find the password by using a combination of lowercase letters, uppercase letters, special characters or symbols, and numbers. Such combinations make it difficult for brute force attacks.
The third golden rule is to ensure never to use memorable keyboard paths. For example, if you are using special characters, do not use the sequence @#$%^&*(). These characters occur in that exact sequence on your keyboard from left to right.
Similarly, if you are using numbers, you should not use 123456. There is no need to explain the sequence here!
The fourth golden rule is to never use common substitutions. For example, replacing e with 3; o with 0; etc. should be avoided. For instance, if your password is bookworm157, you may have a tendency of using b00kw0rm157.
Such substitutions are too easy to guess, because somewhere some hacker has already created those rules and those rules are now being widely used.
Follow these four golden rules, and you can get a password that can easily stop brute force attacks.
Step 3: Can your password prevent dictionary attacks?
I explained this earlier. Use four or five uncommon words (that are not on the list of top 10,000 or 20,000 English words) without white spaces between them.
This increases the number of guesses to the total number of possible words you can use to the power of the total number of actual words you are using.
Make it further difficult using capitalizations in between. Throw in a couple of special characters and numbers.
Make life even difficult for hackers by coming up with some word. Invent one word and use it in your password.
A nice example will be:
ImpignorateSerendipity?Honchogula9Biblioklept}
Now notice the breakdown:
Impignorate – an uncommon English word.
Serendipity – an English word not used commonly.
? – a special character
Honchogula – there is no such word. I made it up!
9 – a number
Biblioklept – a very uncommon English word.
} – a special character.
Now notice the password again:
ImpignorateSerendipity?Honchogula9Biblioklept}
Notice how I capitalized the words (colored red), added special characters and a number (colored blue), and introduced a word that doesn’t exist in any dictionary.
Now count the number of characters. There are 47 characters.
Two things happen here:
- The length of the password and the combination of uppercase letters, lowercase letters, number, and special characters makes it nearly impossible for any brute force attack.
- The three unpopular English words with a made-up word and special characters and a number thrown in between makes it impossible for a dictionary attack to crack this password.
Even if the dictionary attack gets the three unpopular words (which is very unlikely), the hacker has to find the order in which they are placed. He or she also needs to figure out the position of capitalization, the position of the number, and the position of the special characters.
No! A dictionary attack cannot crack it.
If you don’t want to go through the trouble of finding the uncommon English words, you can use the names of your favorite historical characters and scientists, or something like that. You may even use the names of brands or local businesses, a word from another language, etc.
For instance, you may use something like:
LothbrokNecatNamhaidOnGort
- Lothbrok was a Viking warrior.
- Necat is Latin for Kills.
- Namhaid is Irish for Enemy.
- On is an English word.
- Gort is Irish for Field.
So, put together in English, the phrase becomes Lothbrok kills enemy on field.
Well, that’s definitely not an accurate translation, but it does get the job done. A dictionary attack cannot find words like those.
The thing here is that the phrase creates a picture in your mind and you use words from different languages and the name of a historical figure to create the phrase.
A dictionary cannot read your mind! Throw in a few special characters here and there and this anti-dictionary-attack password also becomes an anti-brute-force-attack password.
That’s it! You have your perfect password!
But You Can Use the Sentence Method, Too
While using uncommon words, special characters, numbers, capitalizations, or a made-up word, etc. is a great way to go, you can also take the sentence method.
Come up with a sentence that is very personal to you and only you can know about it. For example, your name is say, Peter, and you come with with this sentence:
“Peter’s sister whacks his ass every time they play chess.”
Now shorten it something like this:
PeSiWhHiAsEvTiThPlChess.
In this:
Pe | Peter’s |
Si | Sister |
Wh | Whacks |
Hi | His |
As | Ass |
Ev | Every |
Ti | Time |
Th | They |
Pl | Play |
Chess | Chess |
It will be gibberish for others, but it will make perfect sense for you. Throw in a couple of special characters and a couple of numbers, and you are good to go.
Take another example.
“My Last Rented Apartment in Forgery Street Cost Me USD 500 a Month.”
Shorten it to something like:
MLRAiFSCM$5AM
In this example:
M | My |
L | Last |
R | Rented |
A | Apartment |
i | In |
F | Forgery |
S | Street |
C | Cost |
M | Me |
$ | USD |
5 | 500 |
A | A |
M | Month |
In this example, you take only the first letters of the words in the sentence. Again, it is gibberish for others, but you know what it means, and you will possibly remember it.
Interestingly, you have already included a special character, a lowercase letter, and a number. You can add more of these here and there to make it even more difficult.
These Aren’t Workable, Are They?
While whatever described above is great and interesting, the process isn’t really workable when it comes to generating passwords for dozens of websites.
Imagine this scenario: “You have accounts on 24 different sites and you take any method including the sentence method to create 24 different passwords.”
Can you remember which password corresponds to which website?
This is where you have a few solutions.
Let’s find out.
Solution 1: Password Generator and Password Manager
You can use a password generator to create random strong passwords for different sites. Some antivirus programs like Kaspersky, Avast, etc. allow generating random passwords. Now, put them all in a password manager.
Now create a memorable and personal password using the sentence method or any other method mentioned above. Use that password as your master password for the password manager.
If you are working from home, stick that master password on the wall right in front of your workstation.
Solution 2: Use a Secured Vault
Some antivirus programs like Kaspersky allow you to create password-protected secured vaults right on your computer.
Create passwords and put them on a spreadsheet or notepad or word document, and lock up the document in that password vault.
For the password vault (that opens only with a master password), create a personal and memorable password using one of the methods above.
Solution 3: Put them Offline
This is what I do! I have created new passwords for all sites and services I use and put them on an excel sheet and a text file.
I have then put the files in a separate flash drive. Every time I need a password for a specific site, I turn off the Internet, hook up my flash drive, copy the password and store it temporarily on my computer.
Then disconnect my flash drive from my computer, turn on the Internet and use the password to login. Once I login, I delete the temporarily stored password from my computer.
I know, this method is tedious, but barring today’s Amazon incidence (that happened because of my callousness), my other passwords have never been compromised.
You are truly safe from online threats when you are not connected to the Internet.
That’s the policy I use for dealing with passwords.
Further Security Options
Well, by now you know how to create great passwords and manage dozens of passwords. But is there a way to increase the security even further?
Yes, there is! In fact, you can do two things.
Option 1: Use Two-Factor Authentication
Two-Factor Authentication or TFA is a great way to enhance the security of your accounts. You will typically need a third-party mobile application like Google Authenticator or Authy that will show you a numeric code when you try to login to your online accounts.
The code keeps changing every 30 seconds. You have to activate TFA or 2FA for the services that provide 2FA support.
For instance, Amazon has 2FA. But PayPal doesn’t have TFA.
The websites and services that support 2FA, you need to activate it by scanning a QR code using the authenticator app you have installed on your mobile device. Once you activate, you will get recovery passwords that you can download and keep safely (preferably offline).
In case you lose access to your mobile device, and you cannot use your authenticator app, the recovery passwords will help you to get into your account.
What about the services that do not offer 2FA like PayPal? For that, you have the second option.
Option 2: Use a hardware key
YubIKey – ever heard of this name? It is a state-of-the-art protection device available. It works as a multi-factor authentication that will allow you to access your files and services only and only when you have the physical device available.
Hardware keys are available in various flavors like NFC-enabled, Bluetooth, and USB forms.
Explaining how it works is beyond the scope of this article. So, I will leave it. You can always run a quick Google search or find videos on YouTube that explain how YubiKey works.
Additional Security Measures to Keep in Mind
Here is a quick summary of things you should never do:
- Use public Wi-Fi without a VPN. A VPN will create a secure channel so that you can use your login credentials without fear.
- Never email passwords to anyone.
- Never share passwords via chatting apps like WhatsApp even though they say that all messages are encrypted. WhatsApp chats keep getting leaked!
- Never share your passwords with anyone in the first place. Why would you do that?
- Never go online without an antivirus program installed. Also never use cracked or nulled antivirus programs.
- If other people are using your computer, create separate user accounts for them so that they don’t get access to your files and folder.
Bottom line – BE SAFE! There are vaccines available even for diseases like COVID-19, but there are no vaccines to weed out hackers. They will always be there. That doesn’t mean you won’t stick your neck out of the window. Simply safeguard your neck.